Update Apache HTTP Server to version 2.4.63
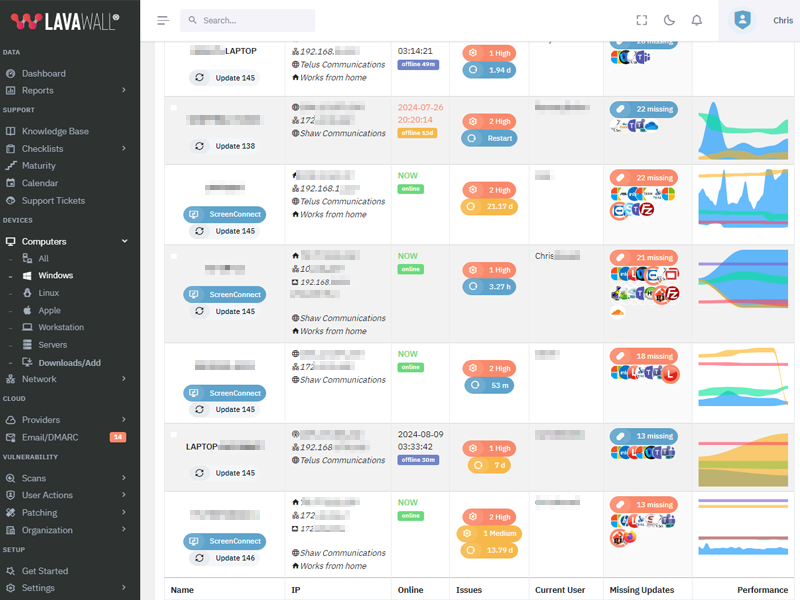
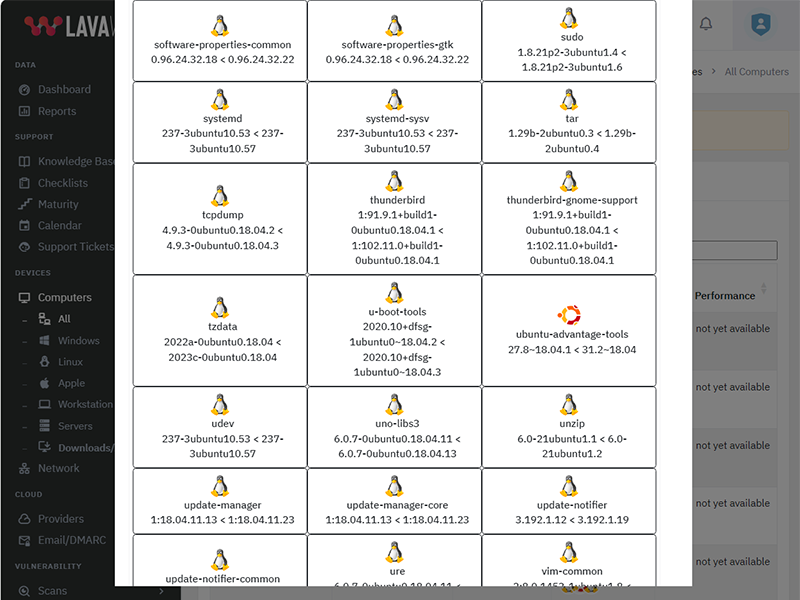
What patches are you missing?
CVE Vulnerabilities for Apache HTTP Server
| CVE | Published | Severity | Details | Exploitability | Impact | Vector |
| CVE‑2024‑40898 | 2024‑07‑18 10:15:03 | HIGH (8) | SSRF in Apache HTTP Server on Windows with mod_rewrite in server/vhost context, allows to potentially leak NTML hashes to a malicious server via SSRF and malicious requests. Users are recommended to upgrade to version 2.4.62 which fixes this issue. | 4 | 4 | NETWORK |
| CVE‑2024‑38477 | 2024‑07‑01 19:15:05 | HIGH (8) | null pointer dereference in mod_proxy in Apache HTTP Server 2.4.59 and earlier allows an attacker to crash the server via a malicious request. Users are recommended to upgrade to version 2.4.60, which fixes this issue. | 4 | 4 | NETWORK |
| CVE‑2024‑38476 | 2024‑07‑01 19:15:05 | CRITICAL (10) | Vulnerability in core of Apache HTTP Server 2.4.59 and earlier are vulnerably to information disclosure, SSRF or local script execution via backend applications whose response headers are malicious or exploitable. Users are recommended to upgrade to version 2.4.60, which fixes this issue. | 4 | 6 | NETWORK |
| CVE‑2024‑38474 | 2024‑07‑01 19:15:05 | CRITICAL (10) | Substitution encoding issue in mod_rewrite in Apache HTTP Server 2.4.59 and earlier allows attacker to execute scripts in directories permitted by the configuration but not directly reachable by any URL or source disclosure of scripts meant to only to be executed as CGI. Users are recommended to upgrade to version 2.4.60, which fixes this issue. Some RewriteRules that capture and substitute unsafely will now fail unless rewrite flag "UnsafeAllow3F" is specified. | 4 | 6 | NETWORK |
| CVE‑2023‑43622 | 2023‑10‑23 07:15:11 | HIGH (8) | An attacker, opening a HTTP/2 connection with an initial window size of 0, was able to block handling of that connection indefinitely in Apache HTTP Server. This could be used to exhaust worker resources in the server, similar to the well known "slow loris" attack pattern. This has been fixed in version 2.4.58, so that such connection are terminated properly after the configured connection timeout. This issue affects Apache HTTP Server: from 2.4.55 through 2.4.57. Users are recommended to upgrade to version 2.4.58, which fixes the issue. | 4 | 4 | NETWORK |
| CVE‑2023‑31122 | 2023‑10‑23 07:15:11 | HIGH (8) | Out-of-bounds Read vulnerability in mod_macro of Apache HTTP Server.This issue affects Apache HTTP Server: through 2.4.57. | 4 | 4 | NETWORK |
| CVE‑2023‑27522 | 2023‑03‑07 16:15:10 | HIGH (8) | HTTP Response Smuggling vulnerability in Apache HTTP Server via mod_proxy_uwsgi. This issue affects Apache HTTP Server: from 2.4.30 through 2.4.55. Special characters in the origin response header can truncate/split the response forwarded to the client. | 4 | 4 | NETWORK |
| CVE‑2023‑25690 | 2023‑03‑07 16:15:09 | CRITICAL (10) | Some mod_proxy configurations on Apache HTTP Server versions 2.4.0 through 2.4.55 allow a HTTP Request Smuggling attack. Configurations are affected when mod_proxy is enabled along with some form of RewriteRule or ProxyPassMatch in which a non-specific pattern matches some portion of the user-supplied request-target (URL) data and is then re-inserted into the proxied request-target using variable substitution. For example, something like: RewriteEngine on RewriteRule "^/here/(.*)" "http://example.com:8080/elsewhere?$1"; [P] ProxyPassReverse /here/ http://example.com:8080/ Request splitting/smuggling could result in bypass of access controls in the proxy server, proxying unintended URLs to existing origin servers, and cache poisoning. Users are recommended to update to at least version 2.4.56 of Apache HTTP Server. | 4 | 6 | NETWORK |
| CVE‑2022‑37436 | 2023‑01‑17 20:15:12 | MEDIUM (5) | Prior to Apache HTTP Server 2.4.55, a malicious backend can cause the response headers to be truncated early, resulting in some headers being incorporated into the response body. If the later headers have any security purpose, they will not be interpreted by the client. | 4 | 1 | NETWORK |
| CVE‑2022‑36760 | 2023‑01‑17 20:15:12 | CRITICAL (9) | Inconsistent Interpretation of HTTP Requests ('HTTP Request Smuggling') vulnerability in mod_proxy_ajp of Apache HTTP Server allows an attacker to smuggle requests to the AJP server it forwards requests to. This issue affects Apache HTTP Server Apache HTTP Server 2.4 version 2.4.54 and prior versions. | 2 | 6 | NETWORK |
| CVE‑2022‑31813 | 2022‑06‑09 17:15:10 | CRITICAL (10) | Apache HTTP Server 2.4.53 and earlier may not send the X-Forwarded-* headers to the origin server based on client side Connection header hop-by-hop mechanism. This may be used to bypass IP based authentication on the origin server/application. | 4 | 6 | NETWORK |
| CVE‑2022‑30556 | 2022‑06‑09 17:15:10 | HIGH (8) | Apache HTTP Server 2.4.53 and earlier may return lengths to applications calling r:wsread() that point past the end of the storage allocated for the buffer. | 4 | 4 | NETWORK |
| CVE‑2022‑30522 | 2022‑06‑09 17:15:10 | HIGH (8) | If Apache HTTP Server 2.4.53 is configured to do transformations with mod_sed in contexts where the input to mod_sed may be very large, mod_sed may make excessively large memory allocations and trigger an abort. | 4 | 4 | NETWORK |
| CVE‑2022‑29404 | 2022‑06‑09 17:15:09 | HIGH (8) | In Apache HTTP Server 2.4.53 and earlier, a malicious request to a lua script that calls r:parsebody(0) may cause a denial of service due to no default limit on possible input size. | 4 | 4 | NETWORK |
| CVE‑2022‑28615 | 2022‑06‑09 17:15:09 | CRITICAL (9) | Apache HTTP Server 2.4.53 and earlier may crash or disclose information due to a read beyond bounds in ap_strcmp_match() when provided with an extremely large input buffer. While no code distributed with the server can be coerced into such a call, third-party modules or lua scripts that use ap_strcmp_match() may hypothetically be affected. | 4 | 5 | NETWORK |
| CVE‑2022‑28614 | 2022‑06‑09 17:15:09 | MEDIUM (5) | The ap_rwrite() function in Apache HTTP Server 2.4.53 and earlier may read unintended memory if an attacker can cause the server to reflect very large input using ap_rwrite() or ap_rputs(), such as with mod_luas r:puts() function. Modules compiled and distributed separately from Apache HTTP Server that use the 'ap_rputs' function and may pass it a very large (INT_MAX or larger) string must be compiled against current headers to resolve the issue. | 4 | 1 | NETWORK |
| CVE‑2022‑28330 | 2022‑06‑09 17:15:09 | MEDIUM (5) | Apache HTTP Server 2.4.53 and earlier on Windows may read beyond bounds when configured to process requests with the mod_isapi module. | 4 | 1 | NETWORK |
| CVE‑2022‑26377 | 2022‑06‑09 17:15:09 | HIGH (8) | Inconsistent Interpretation of HTTP Requests ('HTTP Request Smuggling') vulnerability in mod_proxy_ajp of Apache HTTP Server allows an attacker to smuggle requests to the AJP server it forwards requests to. This issue affects Apache HTTP Server Apache HTTP Server 2.4 version 2.4.53 and prior versions. | 4 | 4 | NETWORK |
| CVE‑2022‑23943 | 2022‑03‑14 11:15:09 | CRITICAL (10) | Out-of-bounds Write vulnerability in mod_sed of Apache HTTP Server allows an attacker to overwrite heap memory with possibly attacker provided data. This issue affects Apache HTTP Server 2.4 version 2.4.52 and prior versions. | 4 | 6 | NETWORK |
| CVE‑2022‑22721 | 2022‑03‑14 11:15:09 | CRITICAL (9) | If LimitXMLRequestBody is set to allow request bodies larger than 350MB (defaults to 1M) on 32 bit systems an integer overflow happens which later causes out of bounds writes. This issue affects Apache HTTP Server 2.4.52 and earlier. | 4 | 5 | NETWORK |
| CVE‑2022‑22720 | 2022‑03‑14 11:15:09 | CRITICAL (10) | Apache HTTP Server 2.4.52 and earlier fails to close inbound connection when errors are encountered discarding the request body, exposing the server to HTTP Request Smuggling | 4 | 6 | NETWORK |
| CVE‑2022‑22719 | 2022‑03‑14 11:15:09 | HIGH (8) | A carefully crafted request body can cause a read to a random memory area which could cause the process to crash. This issue affects Apache HTTP Server 2.4.52 and earlier. | 4 | 4 | NETWORK |
| CVE‑2021‑44790 | 2021‑12‑20 12:15:07 | CRITICAL (10) | A carefully crafted request body can cause a buffer overflow in the mod_lua multipart parser (r:parsebody() called from Lua scripts). The Apache httpd team is not aware of an exploit for the vulnerabilty though it might be possible to craft one. This issue affects Apache HTTP Server 2.4.51 and earlier. | 4 | 6 | NETWORK |
| CVE‑2021‑44224 | 2021‑12‑20 12:15:07 | HIGH (8) | A crafted URI sent to httpd configured as a forward proxy (ProxyRequests on) can cause a crash (NULL pointer dereference) or, for configurations mixing forward and reverse proxy declarations, can allow for requests to be directed to a declared Unix Domain Socket endpoint (Server Side Request Forgery). This issue affects Apache HTTP Server 2.4.7 up to 2.4.51 (included). | 4 | 4 | NETWORK |
| CVE‑2021‑42013 | 2021‑10‑07 16:15:09 | CRITICAL (10) | It was found that the fix for CVE-2021-41773 in Apache HTTP Server 2.4.50 was insufficient. An attacker could use a path traversal attack to map URLs to files outside the directories configured by Alias-like directives. If files outside of these directories are not protected by the usual default configuration "require all denied", these requests can succeed. If CGI scripts are also enabled for these aliased pathes, this could allow for remote code execution. This issue only affects Apache 2.4.49 and Apache 2.4.50 and not earlier versions. | 4 | 6 | NETWORK |
| CVE‑2021‑41773 | 2021‑10‑05 09:15:08 | HIGH (8) | A flaw was found in a change made to path normalization in Apache HTTP Server 2.4.49. An attacker could use a path traversal attack to map URLs to files outside the directories configured by Alias-like directives. If files outside of these directories are not protected by the usual default configuration "require all denied", these requests can succeed. If CGI scripts are also enabled for these aliased pathes, this could allow for remote code execution. This issue is known to be exploited in the wild. This issue only affects Apache 2.4.49 and not earlier versions. The fix in Apache HTTP Server 2.4.50 was found to be incomplete, see CVE-2021-42013. | 4 | 4 | NETWORK |
| CVE‑2021‑40438 | 2021‑09‑16 15:15:08 | CRITICAL (9) | A crafted request uri-path can cause mod_proxy to forward the request to an origin server choosen by the remote user. This issue affects Apache HTTP Server 2.4.48 and earlier. | 2 | 6 | NETWORK |
| CVE‑2021‑39275 | 2021‑09‑16 15:15:08 | CRITICAL (10) | ap_escape_quotes() may write beyond the end of a buffer when given malicious input. No included modules pass untrusted data to these functions, but third-party / external modules may. This issue affects Apache HTTP Server 2.4.48 and earlier. | 4 | 6 | NETWORK |
| CVE‑2021‑36160 | 2021‑09‑16 15:15:07 | HIGH (8) | A carefully crafted request uri-path can cause mod_proxy_uwsgi to read above the allocated memory and crash (DoS). This issue affects Apache HTTP Server versions 2.4.30 to 2.4.48 (inclusive). | 4 | 4 | NETWORK |
| CVE‑2021‑34798 | 2021‑09‑16 15:15:07 | HIGH (8) | Malformed requests may cause the server to dereference a NULL pointer. This issue affects Apache HTTP Server 2.4.48 and earlier. | 4 | 4 | NETWORK |
| CVE‑2021‑33193 | 2021‑08‑16 08:15:11 | HIGH (8) | A crafted method sent through HTTP/2 will bypass validation and be forwarded by mod_proxy, which can lead to request splitting or cache poisoning. This issue affects Apache HTTP Server 2.4.17 to 2.4.48. | 4 | 4 | NETWORK |
| CVE‑2021‑32792 | 2021‑07‑26 17:15:08 | MEDIUM (6) | mod_auth_openidc is an authentication/authorization module for the Apache 2.x HTTP server that functions as an OpenID Connect Relying Party, authenticating users against an OpenID Connect Provider. In mod_auth_openidc before version 2.4.9, there is an XSS vulnerability in when using `OIDCPreservePost On`. | 3 | 3 | NETWORK |
| CVE‑2021‑32791 | 2021‑07‑26 17:15:08 | MEDIUM (6) | mod_auth_openidc is an authentication/authorization module for the Apache 2.x HTTP server that functions as an OpenID Connect Relying Party, authenticating users against an OpenID Connect Provider. In mod_auth_openidc before version 2.4.9, the AES GCM encryption in mod_auth_openidc uses a static IV and AAD. It is important to fix because this creates a static nonce and since aes-gcm is a stream cipher, this can lead to known cryptographic issues, since the same key is being reused. From 2.4.9 onwards this has been patched to use dynamic values through usage of cjose AES encryption routines. | 2 | 4 | NETWORK |
| CVE‑2021‑32786 | 2021‑07‑22 22:15:08 | MEDIUM (6) | mod_auth_openidc is an authentication/authorization module for the Apache 2.x HTTP server that functions as an OpenID Connect Relying Party, authenticating users against an OpenID Connect Provider. In versions prior to 2.4.9, `oidc_validate_redirect_url()` does not parse URLs the same way as most browsers do. As a result, this function can be bypassed and leads to an Open Redirect vulnerability in the logout functionality. This bug has been fixed in version 2.4.9 by replacing any backslash of the URL to redirect with slashes to address a particular breaking change between the different specifications (RFC2396 / RFC3986 and WHATWG). As a workaround, this vulnerability can be mitigated by configuring `mod_auth_openidc` to only allow redirection whose destination matches a given regular expression. | 3 | 3 | NETWORK |
| CVE‑2021‑32785 | 2021‑07‑22 22:15:08 | HIGH (8) | mod_auth_openidc is an authentication/authorization module for the Apache 2.x HTTP server that functions as an OpenID Connect Relying Party, authenticating users against an OpenID Connect Provider. When mod_auth_openidc versions prior to 2.4.9 are configured to use an unencrypted Redis cache (`OIDCCacheEncrypt off`, `OIDCSessionType server-cache`, `OIDCCacheType redis`), `mod_auth_openidc` wrongly performed argument interpolation before passing Redis requests to `hiredis`, which would perform it again and lead to an uncontrolled format string bug. Initial assessment shows that this bug does not appear to allow gaining arbitrary code execution, but can reliably provoke a denial of service by repeatedly crashing the Apache workers. This bug has been corrected in version 2.4.9 by performing argument interpolation only once, using the `hiredis` API. As a workaround, this vulnerability can be mitigated by setting `OIDCCacheEncrypt` to `on`, as cache keys are cryptographically hashed before use when this option is enabled. | 4 | 4 | NETWORK |
| CVE‑2021‑31618 | 2021‑06‑15 09:15:08 | HIGH (8) | Apache HTTP Server protocol handler for the HTTP/2 protocol checks received request headers against the size limitations as configured for the server and used for the HTTP/1 protocol as well. On violation of these restrictions and HTTP response is sent to the client with a status code indicating why the request was rejected. This rejection response was not fully initialised in the HTTP/2 protocol handler if the offending header was the very first one received or appeared in a a footer. This led to a NULL pointer dereference on initialised memory, crashing reliably the child process. Since such a triggering HTTP/2 request is easy to craft and submit, this can be exploited to DoS the server. This issue affected mod_http2 1.15.17 and Apache HTTP Server version 2.4.47 only. Apache HTTP Server 2.4.47 was never released. | 4 | 4 | NETWORK |
| CVE‑2021‑30641 | 2021‑06‑10 07:15:08 | MEDIUM (5) | Apache HTTP Server versions 2.4.39 to 2.4.46 Unexpected matching behavior with 'MergeSlashes OFF' | 4 | 1 | NETWORK |
| CVE‑2021‑26691 | 2021‑06‑10 07:15:08 | CRITICAL (10) | In Apache HTTP Server versions 2.4.0 to 2.4.46 a specially crafted SessionHeader sent by an origin server could cause a heap overflow | 4 | 6 | NETWORK |
| CVE‑2021‑26690 | 2021‑06‑10 07:15:08 | HIGH (8) | Apache HTTP Server versions 2.4.0 to 2.4.46 A specially crafted Cookie header handled by mod_session can cause a NULL pointer dereference and crash, leading to a possible Denial Of Service | 4 | 4 | NETWORK |
| CVE‑2020‑9490 | 2020‑08‑07 16:15:12 | HIGH (8) | Apache HTTP Server versions 2.4.20 to 2.4.43. A specially crafted value for the 'Cache-Digest' header in a HTTP/2 request would result in a crash when the server actually tries to HTTP/2 PUSH a resource afterwards. Configuring the HTTP/2 feature via "H2Push off" will mitigate this vulnerability for unpatched servers. | 4 | 4 | NETWORK |
| CVE‑2020‑35452 | 2021‑06‑10 07:15:07 | HIGH (7) | Apache HTTP Server versions 2.4.0 to 2.4.46 A specially crafted Digest nonce can cause a stack overflow in mod_auth_digest. There is no report of this overflow being exploitable, nor the Apache HTTP Server team could create one, though some particular compiler and/or compilation option might make it possible, with limited consequences anyway due to the size (a single byte) and the value (zero byte) of the overflow | 4 | 3 | NETWORK |
| CVE‑2020‑1934 | 2020‑04‑01 20:15:15 | MEDIUM (5) | In Apache HTTP Server 2.4.0 to 2.4.41, mod_proxy_ftp may use uninitialized memory when proxying to a malicious FTP server. | 4 | 1 | NETWORK |
| CVE‑2020‑1927 | 2020‑04‑02 00:15:13 | MEDIUM (6) | In Apache HTTP Server 2.4.0 to 2.4.41, redirects configured with mod_rewrite that were intended to be self-referential might be fooled by encoded newlines and redirect instead to an an unexpected URL within the request URL. | 3 | 3 | NETWORK |
| CVE‑2020‑13950 | 2021‑06‑10 07:15:07 | HIGH (8) | Apache HTTP Server versions 2.4.41 to 2.4.46 mod_proxy_http can be made to crash (NULL pointer dereference) with specially crafted requests using both Content-Length and Transfer-Encoding headers, leading to a Denial of Service | 4 | 4 | NETWORK |
| CVE‑2020‑13938 | 2021‑06‑10 07:15:07 | MEDIUM (6) | Apache HTTP Server versions 2.4.0 to 2.4.46 Unprivileged local users can stop httpd on Windows | 2 | 4 | LOCAL |
| CVE‑2020‑11993 | 2020‑08‑07 16:15:12 | HIGH (8) | Apache HTTP Server versions 2.4.20 to 2.4.43 When trace/debug was enabled for the HTTP/2 module and on certain traffic edge patterns, logging statements were made on the wrong connection, causing concurrent use of memory pools. Configuring the LogLevel of mod_http2 above "info" will mitigate this vulnerability for unpatched servers. | 4 | 4 | NETWORK |
| CVE‑2020‑11985 | 2020‑08‑07 16:15:12 | MEDIUM (5) | IP address spoofing when proxying using mod_remoteip and mod_rewrite For configurations using proxying with mod_remoteip and certain mod_rewrite rules, an attacker could spoof their IP address for logging and PHP scripts. Note this issue was fixed in Apache HTTP Server 2.4.24 but was retrospectively allocated a low severity CVE in 2020. | 4 | 1 | NETWORK |
| CVE‑2020‑11984 | 2020‑08‑07 16:15:12 | CRITICAL (10) | Apache HTTP server 2.4.32 to 2.4.44 mod_proxy_uwsgi info disclosure and possible RCE | 4 | 6 | NETWORK |
| CVE‑2019‑17567 | 2021‑06‑10 07:15:07 | MEDIUM (5) | Apache HTTP Server versions 2.4.6 to 2.4.46 mod_proxy_wstunnel configured on an URL that is not necessarily Upgraded by the origin server was tunneling the whole connection regardless, thus allowing for subsequent requests on the same connection to pass through with no HTTP validation, authentication or authorization possibly configured. | 4 | 1 | NETWORK |
| CVE‑2019‑10098 | 2019‑09‑25 17:15:10 | MEDIUM (6) | In Apache HTTP server 2.4.0 to 2.4.39, Redirects configured with mod_rewrite that were intended to be self-referential might be fooled by encoded newlines and redirect instead to an unexpected URL within the request URL. | 3 | 3 | NETWORK |
| CVE‑2019‑10097 | 2019‑09‑26 16:15:11 | HIGH (7) | In Apache HTTP Server 2.4.32-2.4.39, when mod_remoteip was configured to use a trusted intermediary proxy server using the "PROXY" protocol, a specially crafted PROXY header could trigger a stack buffer overflow or NULL pointer deference. This vulnerability could only be triggered by a trusted proxy and not by untrusted HTTP clients. | 1 | 6 | NETWORK |
| CVE‑2019‑10092 | 2019‑09‑26 16:15:11 | MEDIUM (6) | In Apache HTTP Server 2.4.0-2.4.39, a limited cross-site scripting issue was reported affecting the mod_proxy error page. An attacker could cause the link on the error page to be malformed and instead point to a page of their choice. This would only be exploitable where a server was set up with proxying enabled but was misconfigured in such a way that the Proxy Error page was displayed. | 3 | 3 | NETWORK |
| CVE‑2019‑10082 | 2019‑09‑26 16:15:11 | CRITICAL (9) | In Apache HTTP Server 2.4.18-2.4.39, using fuzzed network input, the http/2 session handling could be made to read memory after being freed, during connection shutdown. | 4 | 5 | NETWORK |
| CVE‑2019‑0220 | 2019‑06‑11 21:29:01 | MEDIUM (5) | A vulnerability was found in Apache HTTP Server 2.4.0 to 2.4.38. When the path component of a request URL contains multiple consecutive slashes ('/'), directives such as LocationMatch and RewriteRule must account for duplicates in regular expressions while other aspects of the servers processing will implicitly collapse them. | 0 | 0 | NETWORK |
| CVE‑2019‑0217 | 2019‑04‑08 21:29:01 | HIGH (8) | In Apache HTTP Server 2.4 release 2.4.38 and prior, a race condition in mod_auth_digest when running in a threaded server could allow a user with valid credentials to authenticate using another username, bypassing configured access control restrictions. | 2 | 6 | NETWORK |
| CVE‑2019‑0215 | 2019‑04‑08 20:29:10 | MEDIUM (6) | In Apache HTTP Server 2.4 releases 2.4.37 and 2.4.38, a bug in mod_ssl when using per-location client certificate verification with TLSv1.3 allowed a client to bypass configured access control restrictions. | 0 | 0 | NETWORK |
| CVE‑2019‑0211 | 2019‑04‑08 22:29:00 | HIGH (7) | In Apache HTTP Server 2.4 releases 2.4.17 to 2.4.38, with MPM event, worker or prefork, code executing in less-privileged child processes or threads (including scripts executed by an in-process scripting interpreter) could execute arbitrary code with the privileges of the parent process (usually root) by manipulating the scoreboard. Non-Unix systems are not affected. | 0 | 0 | LOCAL |
| CVE‑2019‑0197 | 2019‑06‑11 22:29:04 | MEDIUM (4) | A vulnerability was found in Apache HTTP Server 2.4.34 to 2.4.38. When HTTP/2 was enabled for a http: host or H2Upgrade was enabled for h2 on a https: host, an Upgrade request from http/1.1 to http/2 that was not the first request on a connection could lead to a misconfiguration and crash. Server that never enabled the h2 protocol or that only enabled it for https: and did not set "H2Upgrade on" are unaffected by this issue. | 2 | 3 | NETWORK |
| CVE‑2019‑0196 | 2019‑06‑11 22:29:04 | MEDIUM (5) | A vulnerability was found in Apache HTTP Server 2.4.17 to 2.4.38. Using fuzzed network input, the http/2 request handling could be made to access freed memory in string comparison when determining the method of a request and thus process the request incorrectly. | 0 | 0 | NETWORK |
| CVE‑2019‑0190 | 2019‑01‑30 22:29:00 | HIGH (8) | A bug exists in the way mod_ssl handled client renegotiations. A remote attacker could send a carefully crafted request that would cause mod_ssl to enter a loop leading to a denial of service. This bug can be only triggered with Apache HTTP Server version 2.4.37 when using OpenSSL version 1.1.1 or later, due to an interaction in changes to handling of renegotiation attempts. | 4 | 4 | NETWORK |
| CVE‑2018‑8011 | 2018‑07‑18 14:29:00 | MEDIUM (5) | By specially crafting HTTP requests, the mod_md challenge handler would dereference a NULL pointer and cause the child process to segfault. This could be used to DoS the server. Fixed in Apache HTTP Server 2.4.34 (Affected 2.4.33). | 0 | 0 | NETWORK |
| CVE‑2018‑17199 | 2019‑01‑30 22:29:00 | MEDIUM (5) | In Apache HTTP Server 2.4 release 2.4.37 and prior, mod_session checks the session expiry time before decoding the session. This causes session expiry time to be ignored for mod_session_cookie sessions since the expiry time is loaded when the session is decoded. | 0 | 0 | NETWORK |
| CVE‑2018‑17189 | 2019‑01‑30 22:29:00 | MEDIUM (5) | In Apache HTTP server versions 2.4.37 and prior, by sending request bodies in a slow loris way to plain resources, the h2 stream for that request unnecessarily occupied a server thread cleaning up that incoming data. This affects only HTTP/2 (mod_http2) connections. | 4 | 1 | NETWORK |
| CVE‑2018‑1333 | 2018‑06‑18 18:29:00 | MEDIUM (5) | By specially crafting HTTP/2 requests, workers would be allocated 60 seconds longer than necessary, leading to worker exhaustion and a denial of service. Fixed in Apache HTTP Server 2.4.34 (Affected 2.4.18-2.4.30,2.4.33). | 0 | 0 | NETWORK |
| CVE‑2018‑1312 | 2018‑03‑26 15:29:01 | CRITICAL (10) | In Apache httpd 2.2.0 to 2.4.29, when generating an HTTP Digest authentication challenge, the nonce sent to prevent reply attacks was not correctly generated using a pseudo-random seed. In a cluster of servers using a common Digest authentication configuration, HTTP requests could be replayed across servers by an attacker without detection. | 4 | 6 | NETWORK |
| CVE‑2018‑1303 | 2018‑03‑26 15:29:01 | MEDIUM (5) | A specially crafted HTTP request header could have crashed the Apache HTTP Server prior to version 2.4.30 due to an out of bound read while preparing data to be cached in shared memory. It could be used as a Denial of Service attack against users of mod_cache_socache. The vulnerability is considered as low risk since mod_cache_socache is not widely used, mod_cache_disk is not concerned by this vulnerability. | 0 | 0 | NETWORK |
| CVE‑2018‑1302 | 2018‑03‑26 15:29:00 | MEDIUM (4) | When an HTTP/2 stream was destroyed after being handled, the Apache HTTP Server prior to version 2.4.30 could have written a NULL pointer potentially to an already freed memory. The memory pools maintained by the server make this vulnerability hard to trigger in usual configurations, the reporter and the team could not reproduce it outside debug builds, so it is classified as low risk. | 0 | 0 | NETWORK |
| CVE‑2018‑1301 | 2018‑03‑26 15:29:00 | MEDIUM (4) | A specially crafted request could have crashed the Apache HTTP Server prior to version 2.4.30, due to an out of bound access after a size limit is reached by reading the HTTP header. This vulnerability is considered very hard if not impossible to trigger in non-debug mode (both log and build level), so it is classified as low risk for common server usage. | 0 | 0 | NETWORK |
| CVE‑2018‑1283 | 2018‑03‑26 15:29:00 | LOW (4) | In Apache httpd 2.4.0 to 2.4.29, when mod_session is configured to forward its session data to CGI applications (SessionEnv on, not the default), a remote user may influence their content by using a "Session" header. This comes from the "HTTP_SESSION" variable name used by mod_session to forward its data to CGIs, since the prefix "HTTP_" is also used by the Apache HTTP Server to pass HTTP header fields, per CGI specifications. | 0 | 0 | NETWORK |
| CVE‑2018‑11763 | 2018‑09‑25 21:29:00 | MEDIUM (4) | In Apache HTTP Server 2.4.17 to 2.4.34, by sending continuous, large SETTINGS frames a client can occupy a connection, server thread and CPU time without any connection timeout coming to effect. This affects only HTTP/2 connections. A possible mitigation is to not enable the h2 protocol. | 0 | 0 | NETWORK |
| CVE‑2017‑9798 | 2017‑09‑18 15:29:00 | HIGH (8) | Apache httpd allows remote attackers to read secret data from process memory if the Limit directive can be set in a user's .htaccess file, or if httpd.conf has certain misconfigurations, aka Optionsbleed. This affects the Apache HTTP Server through 2.2.34 and 2.4.x through 2.4.27. The attacker sends an unauthenticated OPTIONS HTTP request when attempting to read secret data. This is a use-after-free issue and thus secret data is not always sent, and the specific data depends on many factors including configuration. Exploitation with .htaccess can be blocked with a patch to the ap_limit_section function in server/core.c. | 4 | 4 | NETWORK |
| CVE‑2017‑9789 | 2017‑07‑13 16:29:00 | MEDIUM (5) | When under stress, closing many connections, the HTTP/2 handling code in Apache httpd 2.4.26 would sometimes access memory after it has been freed, resulting in potentially erratic behaviour. | 0 | 0 | NETWORK |
| CVE‑2017‑9788 | 2017‑07‑13 16:29:00 | MEDIUM (6) | In Apache httpd before 2.2.34 and 2.4.x before 2.4.27, the value placeholder in [Proxy-]Authorization headers of type 'Digest' was not initialized or reset before or between successive key=value assignments by mod_auth_digest. Providing an initial key with no '=' assignment could reflect the stale value of uninitialized pool memory used by the prior request, leading to leakage of potentially confidential information, and a segfault in other cases resulting in denial of service. | 0 | 0 | NETWORK |
| CVE‑2017‑7679 | 2017‑06‑20 01:29:00 | HIGH (8) | In Apache httpd 2.2.x before 2.2.33 and 2.4.x before 2.4.26, mod_mime can read one byte past the end of a buffer when sending a malicious Content-Type response header. | 0 | 0 | NETWORK |
| CVE‑2017‑7668 | 2017‑06‑20 01:29:00 | HIGH (8) | The HTTP strict parsing changes added in Apache httpd 2.2.32 and 2.4.24 introduced a bug in token list parsing, which allows ap_find_token() to search past the end of its input string. By maliciously crafting a sequence of request headers, an attacker may be able to cause a segmentation fault, or to force ap_find_token() to return an incorrect value. | 4 | 4 | NETWORK |
| CVE‑2017‑7659 | 2017‑07‑26 21:29:00 | MEDIUM (5) | A maliciously constructed HTTP/2 request could cause mod_http2 in Apache HTTP Server 2.4.24, 2.4.25 to dereference a NULL pointer and crash the server process. | 0 | 0 | NETWORK |
| CVE‑2017‑3169 | 2017‑06‑20 01:29:00 | HIGH (8) | In Apache httpd 2.2.x before 2.2.33 and 2.4.x before 2.4.26, mod_ssl may dereference a NULL pointer when third-party modules call ap_hook_process_connection() during an HTTP request to an HTTPS port. | 0 | 0 | NETWORK |
| CVE‑2017‑3167 | 2017‑06‑20 01:29:00 | CRITICAL (10) | In Apache httpd 2.2.x before 2.2.33 and 2.4.x before 2.4.26, use of the ap_get_basic_auth_pw() by third-party modules outside of the authentication phase may lead to authentication requirements being bypassed. | 4 | 6 | NETWORK |
| CVE‑2017‑15715 | 2018‑03‑26 15:29:00 | MEDIUM (7) | In Apache httpd 2.4.0 to 2.4.29, the expression specified in <FilesMatch> could match '$' to a newline character in a malicious filename, rather than matching only the end of the filename. This could be exploited in environments where uploads of some files are are externally blocked, but only by matching the trailing portion of the filename. | 0 | 0 | NETWORK |
| CVE‑2017‑15710 | 2018‑03‑26 15:29:00 | MEDIUM (5) | In Apache httpd 2.0.23 to 2.0.65, 2.2.0 to 2.2.34, and 2.4.0 to 2.4.29, mod_authnz_ldap, if configured with AuthLDAPCharsetConfig, uses the Accept-Language header value to lookup the right charset encoding when verifying the user's credentials. If the header value is not present in the charset conversion table, a fallback mechanism is used to truncate it to a two characters value to allow a quick retry (for example, 'en-US' is truncated to 'en'). A header value of less than two characters forces an out of bound write of one NUL byte to a memory location that is not part of the string. In the worst case, quite unlikely, the process would crash which could be used as a Denial of Service attack. In the more likely case, this memory is already reserved for future use and the issue has no effect at all. | 0 | 0 | NETWORK |
| CVE‑2016‑8743 | 2017‑07‑27 21:29:00 | HIGH (8) | Apache HTTP Server, in all releases prior to 2.2.32 and 2.4.25, was liberal in the whitespace accepted from requests and sent in response lines and headers. Accepting these different behaviors represented a security concern when httpd participates in any chain of proxies or interacts with back-end application servers, either through mod_proxy or using conventional CGI mechanisms, and may result in request smuggling, response splitting and cache pollution. | 4 | 4 | NETWORK |
| CVE‑2016‑8740 | 2016‑12‑05 19:59:00 | MEDIUM (5) | The mod_http2 module in the Apache HTTP Server 2.4.17 through 2.4.23, when the Protocols configuration includes h2 or h2c, does not restrict request-header length, which allows remote attackers to cause a denial of service (memory consumption) via crafted CONTINUATION frames in an HTTP/2 request. | 0 | 0 | NETWORK |
| CVE‑2016‑8612 | 2018‑03‑09 20:29:00 | LOW (3) | Apache HTTP Server mod_cluster before version httpd 2.4.23 is vulnerable to an Improper Input Validation in the protocol parsing logic in the load balancer resulting in a Segmentation Fault in the serving httpd process. | 0 | 0 | ADJACENT_NETWORK |
| CVE‑2016‑5387 | 2016‑07‑19 02:00:20 | HIGH (8) | The Apache HTTP Server through 2.4.23 follows RFC 3875 section 4.1.18 and therefore does not protect applications from the presence of untrusted client data in the HTTP_PROXY environment variable, which might allow remote attackers to redirect an application's outbound HTTP traffic to an arbitrary proxy server via a crafted Proxy header in an HTTP request, aka an "httpoxy" issue. NOTE: the vendor states "This mitigation has been assigned the identifier CVE-2016-5387"; in other words, this is not a CVE ID for a vulnerability. | 2 | 6 | NETWORK |
| CVE‑2016‑4979 | 2016‑07‑06 14:59:04 | MEDIUM (5) | The Apache HTTP Server 2.4.18 through 2.4.20, when mod_http2 and mod_ssl are enabled, does not properly recognize the "SSLVerifyClient require" directive for HTTP/2 request authorization, which allows remote attackers to bypass intended access restrictions by leveraging the ability to send multiple requests over a single connection and aborting a renegotiation. | 0 | 0 | NETWORK |
| CVE‑2016‑4975 | 2018‑08‑14 12:29:00 | MEDIUM (4) | Possible CRLF injection allowing HTTP response splitting attacks for sites which use mod_userdir. This issue was mitigated by changes made in 2.4.25 and 2.2.32 which prohibit CR or LF injection into the "Location" or other outbound header key or value. Fixed in Apache HTTP Server 2.4.25 (Affected 2.4.1-2.4.23). Fixed in Apache HTTP Server 2.2.32 (Affected 2.2.0-2.2.31). | 0 | 0 | NETWORK |
| CVE‑2016‑2161 | 2017‑07‑27 21:29:00 | MEDIUM (5) | In Apache HTTP Server versions 2.4.0 to 2.4.23, malicious input to mod_auth_digest can cause the server to crash, and each instance continues to crash even for subsequently valid requests. | 0 | 0 | NETWORK |
| CVE‑2016‑1546 | 2016‑07‑06 14:59:02 | MEDIUM (4) | The Apache HTTP Server 2.4.17 and 2.4.18, when mod_http2 is enabled, does not limit the number of simultaneous stream workers for a single HTTP/2 connection, which allows remote attackers to cause a denial of service (stream-processing outage) via modified flow-control windows. | 0 | 0 | NETWORK |
| CVE‑2016‑0736 | 2017‑07‑27 21:29:00 | MEDIUM (5) | In Apache HTTP Server versions 2.4.0 to 2.4.23, mod_session_crypto was encrypting its data/cookie using the configured ciphers with possibly either CBC or ECB modes of operation (AES256-CBC by default), hence no selectable or builtin authenticated encryption. This made it vulnerable to padding oracle attacks, particularly with CBC. | 0 | 0 | NETWORK |
| CVE‑2015‑3185 | 2015‑07‑20 23:59:04 | MEDIUM (4) | The ap_some_auth_required function in server/request.c in the Apache HTTP Server 2.4.x before 2.4.14 does not consider that a Require directive may be associated with an authorization setting rather than an authentication setting, which allows remote attackers to bypass intended access restrictions in opportunistic circumstances by leveraging the presence of a module that relies on the 2.2 API behavior. | 0 | 0 | NETWORK |
| CVE‑2015‑3184 | 2015‑08‑12 14:59:11 | MEDIUM (5) | mod_authz_svn in Apache Subversion 1.7.x before 1.7.21 and 1.8.x before 1.8.14, when using Apache httpd 2.4.x, does not properly restrict anonymous access, which allows remote anonymous users to read hidden files via the path name. | 0 | 0 | NETWORK |
| CVE‑2015‑3183 | 2015‑07‑20 23:59:03 | MEDIUM (5) | The chunked transfer coding implementation in the Apache HTTP Server before 2.4.14 does not properly parse chunk headers, which allows remote attackers to conduct HTTP request smuggling attacks via a crafted request, related to mishandling of large chunk-size values and invalid chunk-extension characters in modules/http/http_filters.c. | 0 | 0 | NETWORK |
| CVE‑2015‑0253 | 2015‑07‑20 23:59:00 | MEDIUM (5) | The read_request_line function in server/protocol.c in the Apache HTTP Server 2.4.12 does not initialize the protocol structure member, which allows remote attackers to cause a denial of service (NULL pointer dereference and process crash) by sending a request that lacks a method to an installation that enables the INCLUDES filter and has an ErrorDocument 400 directive specifying a local URI. | 0 | 0 | NETWORK |
| CVE‑2015‑0228 | 2015‑03‑08 02:59:00 | MEDIUM (5) | The lua_websocket_read function in lua_request.c in the mod_lua module in the Apache HTTP Server through 2.4.12 allows remote attackers to cause a denial of service (child-process crash) by sending a crafted WebSocket Ping frame after a Lua script has called the wsupgrade function. | 0 | 0 | NETWORK |
| CVE‑2014‑8109 | 2014‑12‑29 23:59:00 | MEDIUM (4) | mod_lua.c in the mod_lua module in the Apache HTTP Server 2.3.x and 2.4.x through 2.4.10 does not support an httpd configuration in which the same Lua authorization provider is used with different arguments within different contexts, which allows remote attackers to bypass intended access restrictions in opportunistic circumstances by leveraging multiple Require directives, as demonstrated by a configuration that specifies authorization for one group to access a certain directory, and authorization for a second group to access a second directory. | 0 | 0 | NETWORK |
| CVE‑2014‑3583 | 2014‑12‑15 18:59:02 | MEDIUM (5) | The handle_headers function in mod_proxy_fcgi.c in the mod_proxy_fcgi module in the Apache HTTP Server 2.4.10 allows remote FastCGI servers to cause a denial of service (buffer over-read and daemon crash) via long response headers. | 0 | 0 | NETWORK |
| CVE‑2014‑3581 | 2014‑10‑10 10:55:07 | MEDIUM (5) | The cache_merge_headers_out function in modules/cache/cache_util.c in the mod_cache module in the Apache HTTP Server before 2.4.11 allows remote attackers to cause a denial of service (NULL pointer dereference and application crash) via an empty HTTP Content-Type header. | 0 | 0 | NETWORK |
| CVE‑2014‑3523 | 2014‑07‑20 11:12:50 | MEDIUM (5) | Memory leak in the winnt_accept function in server/mpm/winnt/child.c in the WinNT MPM in the Apache HTTP Server 2.4.x before 2.4.10 on Windows, when the default AcceptFilter is enabled, allows remote attackers to cause a denial of service (memory consumption) via crafted requests. | 0 | 0 | NETWORK |
| CVE‑2014‑3250 | 2017‑12‑11 17:29:00 | MEDIUM (4) | The default vhost configuration file in Puppet before 3.6.2 does not include the SSLCARevocationCheck directive, which might allow remote attackers to obtain sensitive information via a revoked certificate when a Puppet master runs with Apache 2.4. | 0 | 0 | NETWORK |
| CVE‑2014‑0231 | 2014‑07‑20 11:12:49 | MEDIUM (5) | The mod_cgid module in the Apache HTTP Server before 2.4.10 does not have a timeout mechanism, which allows remote attackers to cause a denial of service (process hang) via a request to a CGI script that does not read from its stdin file descriptor. | 0 | 0 | NETWORK |
| CVE‑2014‑0226 | 2014‑07‑20 11:12:49 | MEDIUM (7) | Race condition in the mod_status module in the Apache HTTP Server before 2.4.10 allows remote attackers to cause a denial of service (heap-based buffer overflow), or possibly obtain sensitive credential information or execute arbitrary code, via a crafted request that triggers improper scoreboard handling within the status_handler function in modules/generators/mod_status.c and the lua_ap_scoreboard_worker function in modules/lua/lua_request.c. | 0 | 0 | NETWORK |
| CVE‑2014‑0118 | 2014‑07‑20 11:12:49 | MEDIUM (4) | The deflate_in_filter function in mod_deflate.c in the mod_deflate module in the Apache HTTP Server before 2.4.10, when request body decompression is enabled, allows remote attackers to cause a denial of service (resource consumption) via crafted request data that decompresses to a much larger size. | 0 | 0 | NETWORK |
| CVE‑2014‑0117 | 2014‑07‑20 11:12:49 | MEDIUM (4) | The mod_proxy module in the Apache HTTP Server 2.4.x before 2.4.10, when a reverse proxy is enabled, allows remote attackers to cause a denial of service (child-process crash) via a crafted HTTP Connection header. | 0 | 0 | NETWORK |
| CVE‑2014‑0098 | 2014‑03‑18 05:18:19 | MEDIUM (5) | The log_cookie function in mod_log_config.c in the mod_log_config module in the Apache HTTP Server before 2.4.8 allows remote attackers to cause a denial of service (segmentation fault and daemon crash) via a crafted cookie that is not properly handled during truncation. | 0 | 0 | NETWORK |
| CVE‑2013‑6438 | 2014‑03‑18 05:18:19 | MEDIUM (5) | The dav_xml_get_cdata function in main/util.c in the mod_dav module in the Apache HTTP Server before 2.4.8 does not properly remove whitespace characters from CDATA sections, which allows remote attackers to cause a denial of service (daemon crash) via a crafted DAV WRITE request. | 0 | 0 | NETWORK |
| CVE‑2013‑5704 | 2014‑04‑15 10:55:11 | MEDIUM (5) | The mod_headers module in the Apache HTTP Server 2.2.22 allows remote attackers to bypass "RequestHeader unset" directives by placing a header in the trailer portion of data sent with chunked transfer coding. NOTE: the vendor states "this is not a security issue in httpd as such." | 0 | 0 | NETWORK |
| CVE‑2013‑5697 | 2013‑09‑30 21:55:10 | HIGH (8) | SQL injection vulnerability in mod_accounting.c in the mod_accounting module 0.5 and earlier for Apache allows remote attackers to execute arbitrary SQL commands via a Host header. | 0 | 0 | NETWORK |
| CVE‑2013‑4365 | 2013‑10‑17 23:55:04 | HIGH (8) | Heap-based buffer overflow in the fcgid_header_bucket_read function in fcgid_bucket.c in the mod_fcgid module before 2.3.9 for the Apache HTTP Server allows remote attackers to have an unspecified impact via unknown vectors. | 0 | 0 | NETWORK |
| CVE‑2013‑4352 | 2014‑07‑20 11:12:49 | MEDIUM (4) | The cache_invalidate function in modules/cache/cache_storage.c in the mod_cache module in the Apache HTTP Server 2.4.6, when a caching forward proxy is enabled, allows remote HTTP servers to cause a denial of service (NULL pointer dereference and daemon crash) via vectors that trigger a missing hostname value. | 0 | 0 | NETWORK |
| CVE‑2013‑2765 | 2013‑07‑15 15:55:01 | MEDIUM (5) | The ModSecurity module before 2.7.4 for the Apache HTTP Server allows remote attackers to cause a denial of service (NULL pointer dereference, process crash, and disk consumption) via a POST request with a large body and a crafted Content-Type header. | 0 | 0 | NETWORK |
| CVE‑2013‑2249 | 2013‑07‑23 17:20:43 | HIGH (8) | mod_session_dbd.c in the mod_session_dbd module in the Apache HTTP Server before 2.4.5 proceeds with save operations for a session without considering the dirty flag and the requirement for a new session ID, which has unspecified impact and remote attack vectors. | 0 | 0 | NETWORK |
| CVE‑2013‑1896 | 2013‑07‑10 20:55:01 | MEDIUM (4) | mod_dav.c in the Apache HTTP Server before 2.2.25 does not properly determine whether DAV is enabled for a URI, which allows remote attackers to cause a denial of service (segmentation fault) via a MERGE request in which the URI is configured for handling by the mod_dav_svn module, but a certain href attribute in XML data refers to a non-DAV URI. | 0 | 0 | NETWORK |
| CVE‑2013‑1862 | 2013‑06‑10 17:55:02 | MEDIUM (5) | mod_rewrite.c in the mod_rewrite module in the Apache HTTP Server 2.2.x before 2.2.25 writes data to a log file without sanitizing non-printable characters, which might allow remote attackers to execute arbitrary commands via an HTTP request containing an escape sequence for a terminal emulator. | 0 | 0 | NETWORK |
| CVE‑2013‑0942 | 2013‑05‑22 13:29:56 | MEDIUM (4) | Cross-site scripting (XSS) vulnerability in EMC RSA Authentication Agent 7.1 before 7.1.1 for Web for Internet Information Services, and 7.1 before 7.1.1 for Web for Apache, allows remote attackers to inject arbitrary web script or HTML via unspecified vectors. | 0 | 0 | NETWORK |
| CVE‑2013‑0941 | 2013‑05‑22 13:29:46 | LOW (2) | EMC RSA Authentication API before 8.1 SP1, RSA Web Agent before 5.3.5 for Apache Web Server, RSA Web Agent before 5.3.5 for IIS, RSA PAM Agent before 7.0, and RSA Agent before 6.1.4 for Microsoft Windows use an improper encryption algorithm and a weak key for maintaining the stored data of the node secret for the SecurID Authentication API, which allows local users to obtain sensitive information via cryptographic attacks on this data. | 0 | 0 | LOCAL |
| CVE‑2012‑4558 | 2013‑02‑26 16:55:01 | MEDIUM (4) | Multiple cross-site scripting (XSS) vulnerabilities in the balancer_handler function in the manager interface in mod_proxy_balancer.c in the mod_proxy_balancer module in the Apache HTTP Server 2.2.x before 2.2.24-dev and 2.4.x before 2.4.4 allow remote attackers to inject arbitrary web script or HTML via a crafted string. | 0 | 0 | NETWORK |
| CVE‑2012‑4557 | 2012‑11‑30 19:55:01 | MEDIUM (5) | The mod_proxy_ajp module in the Apache HTTP Server 2.2.12 through 2.2.21 places a worker node into an error state upon detection of a long request-processing time, which allows remote attackers to cause a denial of service (worker consumption) via an expensive request. | 0 | 0 | NETWORK |
| CVE‑2012‑4360 | 2012‑09‑15 10:37:18 | MEDIUM (4) | Cross-site scripting (XSS) vulnerability in the mod_pagespeed module 0.10.19.1 through 0.10.22.4 for the Apache HTTP Server allows remote attackers to inject arbitrary web script or HTML via unspecified vectors. | 0 | 0 | NETWORK |
| CVE‑2012‑4001 | 2012‑09‑15 10:37:18 | MEDIUM (5) | The mod_pagespeed module before 0.10.22.6 for the Apache HTTP Server does not properly verify its host name, which allows remote attackers to trigger HTTP requests to arbitrary hosts via unspecified vectors, as demonstrated by requests to intranet servers. | 0 | 0 | NETWORK |
| CVE‑2012‑3526 | 2012‑09‑05 23:55:02 | MEDIUM (5) | The reverse proxy add forward module (mod_rpaf) 0.5 and 0.6 for the Apache HTTP Server allows remote attackers to cause a denial of service (server or application crash) via multiple X-Forwarded-For headers in a request. | 0 | 0 | NETWORK |
| CVE‑2012‑3502 | 2012‑08‑22 19:55:02 | MEDIUM (4) | The proxy functionality in (1) mod_proxy_ajp.c in the mod_proxy_ajp module and (2) mod_proxy_http.c in the mod_proxy_http module in the Apache HTTP Server 2.4.x before 2.4.3 does not properly determine the situations that require closing a back-end connection, which allows remote attackers to obtain sensitive information in opportunistic circumstances by reading a response that was intended for a different client. | 0 | 0 | NETWORK |
| CVE‑2012‑3499 | 2013‑02‑26 16:55:01 | MEDIUM (4) | Multiple cross-site scripting (XSS) vulnerabilities in the Apache HTTP Server 2.2.x before 2.2.24-dev and 2.4.x before 2.4.4 allow remote attackers to inject arbitrary web script or HTML via vectors involving hostnames and URIs in the (1) mod_imagemap, (2) mod_info, (3) mod_ldap, (4) mod_proxy_ftp, and (5) mod_status modules. | 0 | 0 | NETWORK |
| CVE‑2012‑2687 | 2012‑08‑22 19:55:02 | LOW (3) | Multiple cross-site scripting (XSS) vulnerabilities in the make_variant_list function in mod_negotiation.c in the mod_negotiation module in the Apache HTTP Server 2.4.x before 2.4.3, when the MultiViews option is enabled, allow remote attackers to inject arbitrary web script or HTML via a crafted filename that is not properly handled during construction of a variant list. | 0 | 0 | NETWORK |
| CVE‑2012‑1181 | 2012‑03‑19 21:55:01 | MEDIUM (5) | fcgid_spawn_ctl.c in the mod_fcgid module 2.3.6 for the Apache HTTP Server does not recognize the FcgidMaxProcessesPerClass directive for a virtual host, which makes it easier for remote attackers to cause a denial of service (memory consumption) via a series of HTTP requests that triggers a process count higher than the intended limit. | 0 | 0 | NETWORK |
| CVE‑2012‑0883 | 2012‑04‑18 10:33:34 | MEDIUM (7) | envvars (aka envvars-std) in the Apache HTTP Server before 2.4.2 places a zero-length directory name in the LD_LIBRARY_PATH, which allows local users to gain privileges via a Trojan horse DSO in the current working directory during execution of apachectl. | 0 | 0 | LOCAL |
| CVE‑2012‑0053 | 2012‑01‑28 04:05:01 | MEDIUM (4) | protocol.c in the Apache HTTP Server 2.2.x through 2.2.21 does not properly restrict header information during construction of Bad Request (aka 400) error documents, which allows remote attackers to obtain the values of HTTPOnly cookies via vectors involving a (1) long or (2) malformed header in conjunction with crafted web script. | 0 | 0 | NETWORK |
| CVE‑2012‑0031 | 2012‑01‑18 20:55:03 | MEDIUM (5) | scoreboard.c in the Apache HTTP Server 2.2.21 and earlier might allow local users to cause a denial of service (daemon crash during shutdown) or possibly have unspecified other impact by modifying a certain type field within a scoreboard shared memory segment, leading to an invalid call to the free function. | 0 | 0 | LOCAL |
| CVE‑2012‑0021 | 2012‑01‑28 04:05:01 | LOW (3) | The log_cookie function in mod_log_config.c in the mod_log_config module in the Apache HTTP Server 2.2.17 through 2.2.21, when a threaded MPM is used, does not properly handle a %{}C format string, which allows remote attackers to cause a denial of service (daemon crash) via a cookie that lacks both a name and a value. | 0 | 0 | NETWORK |
| CVE‑2011‑4415 | 2011‑11‑08 11:55:06 | LOW (1) | The ap_pregsub function in server/util.c in the Apache HTTP Server 2.0.x through 2.0.64 and 2.2.x through 2.2.21, when the mod_setenvif module is enabled, does not restrict the size of values of environment variables, which allows local users to cause a denial of service (memory consumption or NULL pointer dereference) via a .htaccess file with a crafted SetEnvIf directive, in conjunction with a crafted HTTP request header, related to (1) the "len +=" statement and (2) the apr_pcalloc function call, a different vulnerability than CVE-2011-3607. | 0 | 0 | LOCAL |
| CVE‑2011‑4317 | 2011‑11‑30 04:05:59 | MEDIUM (4) | The mod_proxy module in the Apache HTTP Server 1.3.x through 1.3.42, 2.0.x through 2.0.64, and 2.2.x through 2.2.21, when the Revision 1179239 patch is in place, does not properly interact with use of (1) RewriteRule and (2) ProxyPassMatch pattern matches for configuration of a reverse proxy, which allows remote attackers to send requests to intranet servers via a malformed URI containing an @ (at sign) character and a : (colon) character in invalid positions. NOTE: this vulnerability exists because of an incomplete fix for CVE-2011-3368. | 0 | 0 | NETWORK |
| CVE‑2011‑3639 | 2011‑11‑30 04:05:58 | MEDIUM (4) | The mod_proxy module in the Apache HTTP Server 2.0.x through 2.0.64 and 2.2.x before 2.2.18, when the Revision 1179239 patch is in place, does not properly interact with use of (1) RewriteRule and (2) ProxyPassMatch pattern matches for configuration of a reverse proxy, which allows remote attackers to send requests to intranet servers by using the HTTP/0.9 protocol with a malformed URI containing an initial @ (at sign) character. NOTE: this vulnerability exists because of an incomplete fix for CVE-2011-3368. | 0 | 0 | NETWORK |
| CVE‑2011‑3607 | 2011‑11‑08 11:55:06 | MEDIUM (4) | Integer overflow in the ap_pregsub function in server/util.c in the Apache HTTP Server 2.0.x through 2.0.64 and 2.2.x through 2.2.21, when the mod_setenvif module is enabled, allows local users to gain privileges via a .htaccess file with a crafted SetEnvIf directive, in conjunction with a crafted HTTP request header, leading to a heap-based buffer overflow. | 0 | 0 | LOCAL |
| CVE‑2011‑3368 | 2011‑10‑05 22:55:03 | MEDIUM (5) | The mod_proxy module in the Apache HTTP Server 1.3.x through 1.3.42, 2.0.x through 2.0.64, and 2.2.x through 2.2.21 does not properly interact with use of (1) RewriteRule and (2) ProxyPassMatch pattern matches for configuration of a reverse proxy, which allows remote attackers to send requests to intranet servers via a malformed URI containing an initial @ (at sign) character. | 0 | 0 | NETWORK |
| CVE‑2011‑3348 | 2011‑09‑20 05:55:03 | MEDIUM (4) | The mod_proxy_ajp module in the Apache HTTP Server before 2.2.21, when used with mod_proxy_balancer in certain configurations, allows remote attackers to cause a denial of service (temporary "error state" in the backend server) via a malformed HTTP request. | 0 | 0 | NETWORK |
| CVE‑2011‑3192 | 2011‑08‑29 15:55:02 | HIGH (8) | The byterange filter in the Apache HTTP Server 1.3.x, 2.0.x through 2.0.64, and 2.2.x through 2.2.19 allows remote attackers to cause a denial of service (memory and CPU consumption) via a Range header that expresses multiple overlapping ranges, as exploited in the wild in August 2011, a different vulnerability than CVE-2007-0086. | 0 | 0 | NETWORK |
| CVE‑2011‑2688 | 2011‑07‑28 18:55:03 | HIGH (8) | SQL injection vulnerability in mysql/mysql-auth.pl in the mod_authnz_external module 3.2.5 and earlier for the Apache HTTP Server allows remote attackers to execute arbitrary SQL commands via the user field. | 0 | 0 | NETWORK |
| CVE‑2011‑1928 | 2011‑05‑24 23:55:04 | MEDIUM (4) | The fnmatch implementation in apr_fnmatch.c in the Apache Portable Runtime (APR) library 1.4.3 and 1.4.4, and the Apache HTTP Server 2.2.18, allows remote attackers to cause a denial of service (infinite loop) via a URI that does not match unspecified types of wildcard patterns, as demonstrated by attacks against mod_autoindex in httpd when a /*/WEB-INF/ configuration pattern is used. NOTE: this issue exists because of an incorrect fix for CVE-2011-0419. | 0 | 0 | NETWORK |
| CVE‑2011‑1176 | 2011‑03‑29 18:55:02 | MEDIUM (4) | The configuration merger in itk.c in the Steinar H. Gunderson mpm-itk Multi-Processing Module 2.2.11-01 and 2.2.11-02 for the Apache HTTP Server does not properly handle certain configuration sections that specify NiceValue but not AssignUserID, which might allow remote attackers to gain privileges by leveraging the root uid and root gid of an mpm-itk process. | 0 | 0 | NETWORK |
| CVE‑2011‑0419 | 2011‑05‑16 17:55:02 | MEDIUM (4) | Stack consumption vulnerability in the fnmatch implementation in apr_fnmatch.c in the Apache Portable Runtime (APR) library before 1.4.3 and the Apache HTTP Server before 2.2.18, and in fnmatch.c in libc in NetBSD 5.1, OpenBSD 4.8, FreeBSD, Apple Mac OS X 10.6, Oracle Solaris 10, and Android, allows context-dependent attackers to cause a denial of service (CPU and memory consumption) via *? sequences in the first argument, as demonstrated by attacks against mod_autoindex in httpd. | 0 | 0 | NETWORK |
| CVE‑2010‑2791 | 2010‑08‑05 18:17:58 | MEDIUM (5) | mod_proxy in httpd in Apache HTTP Server 2.2.9, when running on Unix, does not close the backend connection if a timeout occurs when reading a response from a persistent connection, which allows remote attackers to obtain a potentially sensitive response intended for a different client in opportunistic circumstances via a normal HTTP request. NOTE: this is the same issue as CVE-2010-2068, but for a different OS and set of affected versions. | 0 | 0 | NETWORK |
| CVE‑2010‑2068 | 2010‑06‑18 16:30:01 | MEDIUM (5) | mod_proxy_http.c in mod_proxy_http in the Apache HTTP Server 2.2.9 through 2.2.15, 2.3.4-alpha, and 2.3.5-alpha on Windows, NetWare, and OS/2, in certain configurations involving proxy worker pools, does not properly detect timeouts, which allows remote attackers to obtain a potentially sensitive response intended for a different client in opportunistic circumstances via a normal HTTP request. | 0 | 0 | NETWORK |
| CVE‑2010‑1623 | 2010‑10‑04 21:00:04 | MEDIUM (5) | Memory leak in the apr_brigade_split_line function in buckets/apr_brigade.c in the Apache Portable Runtime Utility library (aka APR-util) before 1.3.10, as used in the mod_reqtimeout module in the Apache HTTP Server and other software, allows remote attackers to cause a denial of service (memory consumption) via unspecified vectors related to the destruction of an APR bucket. | 0 | 0 | NETWORK |
| CVE‑2010‑1452 | 2010‑07‑28 20:00:01 | MEDIUM (5) | The (1) mod_cache and (2) mod_dav modules in the Apache HTTP Server 2.2.x before 2.2.16 allow remote attackers to cause a denial of service (process crash) via a request that lacks a path. | 0 | 0 | NETWORK |
| CVE‑2010‑0434 | 2010‑03‑05 19:30:01 | MEDIUM (4) | The ap_read_request function in server/protocol.c in the Apache HTTP Server 2.2.x before 2.2.15, when a multithreaded MPM is used, does not properly handle headers in subrequests in certain circumstances involving a parent request that has a body, which might allow remote attackers to obtain sensitive information via a crafted request that triggers access to memory locations associated with an earlier request. | 0 | 0 | NETWORK |
| CVE‑2010‑0425 | 2010‑03‑05 19:30:01 | HIGH (10) | modules/arch/win32/mod_isapi.c in mod_isapi in the Apache HTTP Server 2.0.37 through 2.0.63, 2.2.0 through 2.2.14, and 2.3.x before 2.3.7, when running on Windows, does not ensure that request processing is complete before calling isapi_unload for an ISAPI .dll module, which allows remote attackers to execute arbitrary code via unspecified vectors related to a crafted request, a reset packet, and "orphaned callback pointers." | 0 | 0 | NETWORK |
| CVE‑2010‑0408 | 2010‑03‑05 16:30:01 | MEDIUM (5) | The ap_proxy_ajp_request function in mod_proxy_ajp.c in mod_proxy_ajp in the Apache HTTP Server 2.2.x before 2.2.15 does not properly handle certain situations in which a client sends no request body, which allows remote attackers to cause a denial of service (backend server outage) via a crafted request, related to use of a 500 error code instead of the appropriate 400 error code. | 0 | 0 | NETWORK |
| CVE‑2010‑0010 | 2010‑02‑02 16:30:02 | MEDIUM (7) | Integer overflow in the ap_proxy_send_fb function in proxy/proxy_util.c in mod_proxy in the Apache HTTP Server before 1.3.42 on 64-bit platforms allows remote origin servers to cause a denial of service (daemon crash) or possibly execute arbitrary code via a large chunk size that triggers a heap-based buffer overflow. | 0 | 0 | NETWORK |
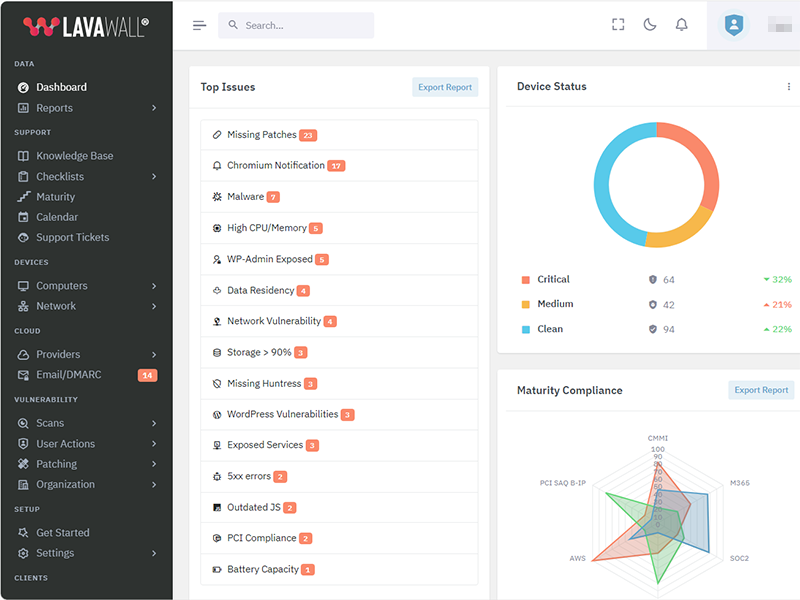
Get the IT stuff done that nobody wants to do.
Patch more applications, achieve compliance, and prevent problems while reducing stress with Lavawall®.
Security First
A security tool by security auditors. From Passkeys and Argon2i to source validation and MVSP principles, Lavawall® has you covered.
Constant Improvement
More features and more security added nearly every day.
More patchable programs added every week
While Ninite and other patching tools have had the same patch offerings for decades, we're monitoring stats to keep adding the most useful programs (currently over 7,438)!
Details matter
From wrapping TLS communications in extra encryption and uninstalling remote support tools when they aren't used to detailed statistical analysis of system and network performance, Lavawall® goes in-depth.
System Reliability
Monitor battery, disk, and process health. Lavawall® combines system health, age, operating system support, memory levels, and other attributes to prioritize systems for replacement.
Human and automated support
Get immediate fixes, user notifications, admin notifications -- and even security-certified human level 3 support when our advanced statistical analysis confirms a problem or anomaly.
| 2025‑03‑10 | 0.12.60.247 | |
| 2025‑03‑04 | 0.12.58.245 | |
| 2025‑03‑03 | 0.12.57.244 | Add TPM complience check and ensure consistent memory gathering in windows/linux/mac |
| 2025‑02‑28 | 0.12.56.243 | Windows RAM reporting and persistent scalability framework enhancements |
| 2025‑02‑27 | 0.12.55.242 | Battery health refinements |
| 2025‑02‑26 | 0.12.54.241 | Add battery health statistics |
| 2025‑02‑26 | 0.12.53.240 | |
| 2025‑01‑29 | 0.12.35.222 | Risk score refinements |
| 2025‑01‑17 | 0.12.29.216 | Enhanced compliance and non-standard AV |
| 2025‑01‑13 | 0.12.28.215 | Improved process graphs |
| 2025‑01‑07 | 0.12.27.214 | Antivirus details, compliance |
| 2024‑12‑27 | 0.12.24.211 | |
| 2024‑12‑02 | 0.12.19.206 | |
| 2024‑11‑22 | 0.12.18.205 | |
| 2024‑10‑30 | 0.12.8.195 | Mac update refinements |
| 2024‑10‑25 | 0.12.3.190 | |
| 2024‑10‑21 | 0.12.0.187 | Macos implementaiton, linux and windows improvements |
| 2024‑10‑16 | 0.11.128.186 | Linux stats and system information improvements, improvements for application shutdown |
| 2024‑09‑12 | 0.11.113.171 | CPU Optimizations and Packages reliability improvements |
| 2024‑09‑05 | 0.11.106.164 | Phased deployment enhancements |
| 2024‑09‑04 | 0.11.103.161 | |
| 2024‑09‑02 | 0.11.102.160 | CPU Optimizations and Packages reliability improvements |
| 2024‑08‑30 | 0.11.99.157 | CPU Optimizations and Packages reliability improvements |
| 2024‑08‑29 | 0.11.98.156 | CPU utilization and console event optimization |
| 2024‑08‑28 | 0.11.97.155 | Reliability to detect unusual updates like redistributables. |
| 2024‑08‑27 | 0.11.96.154 | |
| 2024‑08‑26 | 0.11.95.153 | Faster response for reboot requests |
| 2024‑08‑20 | 0.11.92.150 | Additional package upgrade pre-requisites |
| 2024‑08‑15 | 0.11.89.147 | |
| 2024‑08‑06 | 0.11.87.145 | |
| 2024‑07‑26 | 0.11.83.141 | Add resiliency for MAC duplicates and uptime |
| 2024‑07‑25 | 0.11.82.140 | Changes to facilitate cross-platform use. Bitlocker and Windows key refinements |
| 2024‑07‑15 | 0.11.80.138 | Antivirus and temperature added to configuration checks |
| 2024‑07‑15 | 0.11.79.137 | Add configuration checks for execution policy and secure boot |
| 2024‑07‑11 | 0.11.77.135 | load balancing refinements |
| 2024‑07‑10 | 0.11.76.134 | Add additional load balancing and data residency capabilities, add randomness to recurring task timings to decrease server load |
| 2024‑07‑05 | 0.11.74.132 | changes to graph and residual work on user imporsonation |
| 2024‑07‑04 | 0.11.73.131 | Add configuration checks for execution policy and secure boot. |
| 2024‑07‑03 | 0.11.72.130 | Enhanced event log monitoring |
| 2024‑07‑02 | 0.11.71.129 | Add details to Windows updates, enhanced risk metrics for application patches |
| 2024‑06‑19 | 0.11.65.123 | Update resiliancy and garbage collection |
| 2024‑06‑13 | 0.11.60.118 | Enhanced logging |
| 2024‑06‑12 | 0.11.55.113 | Include the primary drive serial number; MAC addresses for built-in wireless, Bluetooth, and ethernet into the device hash to restore uninstalled and reinstalled devices in cases where the motherboard serial is not unique |
| 2024‑06‑07 | 0.11.54.112 | Patch and package uninstall data addition |
| 2024‑06‑05 | 0.11.47.105 | refine per-user registry application listing |
| 2024‑06‑02 | 0.11.45.103 | uninstall and reinstall refinements, refine local logging, refine self-update and uninstall timing |
| 2024‑05‑30 | 0.11.21.79 | various bug fixes and improvements |
| 2024‑05‑28 | 0.11.16.74 | Error logging, registration, and uninstall improvements. |
| 2024‑05‑24 | 0.11.14.72 | applied changes for devices and login commands, changes for registration as well |
| 2024‑05‑22 | 0.11.13.71 | Add Windows computer model, improve Operating System parsing |
NOTE: changes after June 2024 are incorportated into the Windows Changelog as the codebases for Windows, Linux, and Mac were combined
| 2024‑05‑20 | 253 | Added cleanup of old .json files during a re-install |
| 2024‑05‑13 | 252 | Added apt-get update to install |
| 2024‑05‑06 | 248 | Allow restart to use /var/run/reboot-required if needrestart is not installed |
| 2024‑04‑22 | 239 | Improve internal update and version tracking |
| 2024‑04‑15 | 235 | Add support for Yum packages |
| 2024‑04‑08 | 233 | Align patching with Windows patch reporting |
| 2024‑04‑02 | 228 | Add support for needrestart |
| 2024‑03‑04 | 224 | Schedule restarts |
| 2024‑03‑25 | 221 | Add support for apt packages |
| 2024‑03‑18 | 212 | Implement release management |
| 2024‑03‑11 | 202 | Add user login monitoring |
| 2024‑03‑04 | 189 | Enhance installation reliability |
| 2024‑02‑26 | 187 | Exapand triggers to identify if the instance needs to be restarted |
| 2024‑02‑19 | 146 | Improve compatibility for non-AWS instances |
| 2024‑02‑14 | 138 | Add self-uninstall capabilities |
| 2024‑02‑12 | 135 | Enhance scheduling flexibility |
| 2024‑02‑07 | 132 | Add kernel version tracking |
| 2024‑02‑05 | 124 | Add device hash to cryptographic self-update script validation |
| 2024‑01‑29 | 107 | Enhance encryption of patch data |
| 2024‑01‑22 | 98 | Improve how available storage is calculated |
| 2024‑01‑15 | 97 | Move initial tasks from installation file to sub scripts |
| 2024‑05‑21 | 91 | Improve multi-distribution compatibility |
| 2024‑05‑21 | 79 | Improve encryption reliability |
| 2023‑12‑11 | 68 | Enhance cryptographic validation of new scripts before updating |
| 2023‑11‑20 | 62 | Add inner layer of AES encryption in case TLS inspection doesn't allow for a secure connection |
| 2023‑11‑27 | 56 | Additional base cases for resiliancy |
| 2023‑11‑20 | 54 | Additional headers added to authentication process during installation. |
| 2023‑11‑20 | 53 | Enhanced key management |
| 2023‑11‑15 | 51 | Add insecure installation parameter to allow installation in environments with TLS inspection or other machine-in-the-middle situations. |
| 2023‑11‑06 | 42 | Enhance redundant encryption during installation. |
| 2023‑10‑30 | 33 | Improve install-over compatibility |
| 2023‑10‑23 | 18 | Add reboot configuration and scheduling |
| 2023‑10‑23 | 17 | Add self-updating functionality. |
| 2023‑10‑16 | 15 | Add Linux patching information for apt |
| 2023‑10‑09 | 14 | Collect system information |
| 2023‑10‑09 | 13 | Add Linux distribution information |
| 2023‑09‑30 | 12 | Add memory monitoring |
| 2023‑09‑30 | 10 | Add hardware information |
| 2023‑09‑23 | 9 | Add AWS information |
| 2023‑09‑23 | 8 | Add customized schedule capability for configuration updates |
| 2023‑09‑23 | 7 | Add support for package monitoring using package and dpkg logs |
| 2023‑09‑16 | 6 | Add storage data configuration gathering |
| 2023‑09‑16 | 5 | Add CPU information |
Lavawall® was built from the ground up with these concerns and the Minimum Viable Secure Product requirements in mind.
Some of the controls we implemented include:
- PassKeys as the preferred primary authentication at no additional cost
- Single Sign-on using modern, maintained, and industry-standard protocols for all customers at no additional cost
- Multi-Factor Authentication as a non-negotiable default
- Encrypting communications the same way as TLS again within the TLS tunnel, so we can allow TLS inspection without breaking like Huntress or disclosing security vulnerabilities to eavesdroppers.
- Encouraging external vulnerability reports and customer testing
- Passwords checked against popular disclosed passwords, hashed before they leave your computer, and then stored using Argon2id
- Not requiring the use of passwords at all. We consider them a temporary backup authentication in case you can't use passkeys or SSO.
Lavawall® databases and front-end systems are hosted with AWS in Montréal, Québec, Canada.
We send emails through AWS in Ireland and dedicated servers in Calgary, Alberta, Canada.
We send text messages for additional identity verification through Twilio in the United States.
We store executables and pass requests through Cloudflare at your nearest edge location.
We use Cloudflare for risk management, turnstile, and web application firewall services.
We use LeadPages for landing pages.
We use Google and Facebook for analytics on our public-facing pages, but they do not have access to the console.
We integrate with third-party tools, such as Microsoft, Google, Huntress, Screen Connect, Axcient, and Datto in their respective locations. However, you must initiate these integrations through single sign-on or by enabling them in your Lavawall® console.
Active security by design
Lavawall® is under active development with the latest release including:
7,438+
Monitored Applications
61+
System Metrics
Actively manage your IT with Lavawall®
Patching
Updates Beyond Windows
Lavawall® prevents the 80% of breaches and failed audits due to missing patches and updates.
You can reduce application patching delays from 67 days to nearly immediate with the 7,438+ applications that Lavawall® monitors and patches.
Patch release monitoring
Monitor everything without having to select packages or “managed applications”
Patch impact classification
Standard and optional Windows patches
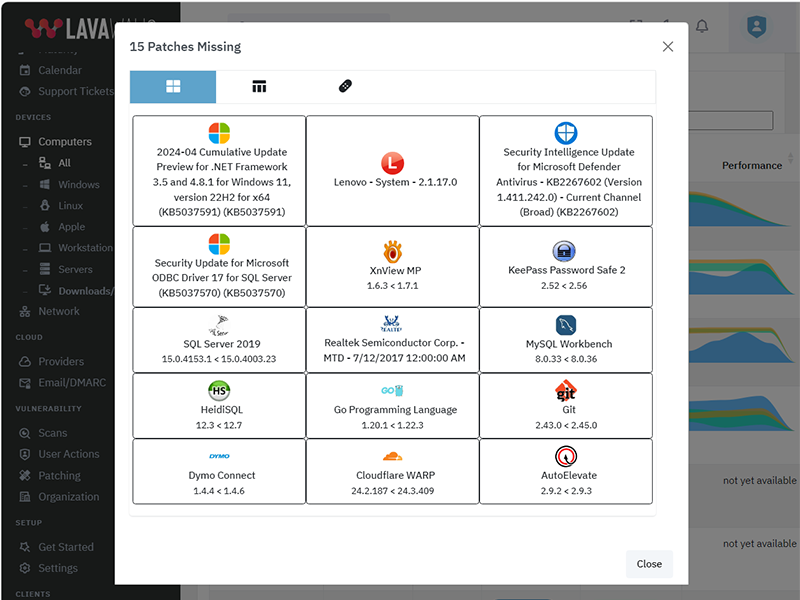
Application Patching
Some of the applications that Lavawall® monitors and audits include:
Logos are property of their respective trademark holders and are not affiliated with ThreeShield or Lavawall. We have not audited the security of most of the listed tools.
The above listing includes products that Lavawall® monitors through public information and/or proprietary statistical analysis.
Although we do have a partner relationship with some of the listed products and companies, they do not necessarily endorse Lavawall® or have integrations with our systems.
Learn More
Flexible Term; Flexible Service
Flexibility for your dynamic business
You need to get your arms around compliance and security and don't want to get locked into “high watermark” monthly invoices or multi-year contracts.
Pay-as-you-need monthly pricing
DIY, full management, and coaching options
Choose the plan that's right for you
Simple pricing. No hidden fees. Advanced features for you business.
Month
Annual
Get 2 months free with Annual!
Minimal
Pay-as-you go. No Commitments.
C$3.25 /computer/Month
C$32.50 /computer/Year
-
1 computer
or 1 of the following cloud integrations:
AWS, Axcient, Datto, Google, Huntress, M365, Sophos Central integrations
(each integration counts as 1 computer) -
50+ application patches
-
30-day Logs
-
Security configuration monitoring
-
Lavawall® support
-
Domain Scanning: C$20/domainDomain Scanning: C$200/domain
-
Level 3+ IT support for IT
-
IT coaching sessions
-
Automatic discount and upgrade to Business Standard at 77 devices
Business Standard
Basic services with 90-day logs
C$250 /Month
C$2,250 /Year
-
150 computers
Additional computers: C$2.50/computerAdditional computers: C$25/computer -
25 domains
Additional domains: C$15/domainAdditional domains: C$150/domain -
AWS, Axcient, Datto, Google, Huntress, M365, Sophos Central integrations
-
7,438+ application patch monitoring
-
90-day Logs
-
Security configuration monitoring
-
Lavawall® support
-
Level 3+ IT support for IT
-
IT coaching sessions
-
Automatic discount and upgrade to Full Service at 950 devices
Full Service
Optimize & audit-ready your IT
$2,250 /Month
$22,500 /Year
-
1,500 computers included
Additional computers: C$2/computerAdditional computers: C$20/computer -
125 domains included
Additional domains: C$10/domainAdditional domains: C$100/domain -
AWS, Axcient, Datto, Google, Huntress, M365, Sophos Central integrations
-
7,438+ application patch monitoring
-
365-day Logs
-
Security configuration monitoring
-
Lavawall® support
-
L3 IT support for IT
-
IT coaching sessions
Frequently Asked Questions
If you can not find answer to your question in our FAQ, you can always contact us or email us. We will answer you shortly!
General Questions
- Two years after a missing Plex Media Server led to the LastPass breach, the
Remote Monitorign and Management (RMM) tools availabel for Manged IT Service Providers (MSPs)
still didn't monitor for it.
Going through industry-specific applications, we noticed many were missing from the big RMM and patching providers. MSPs, insurance providers, and organizations that put their cleints at risk need to know about these risks, which lead to the largest number of critical audit findings and breaches - After 20 years of writing the same audit findings about system configurations, Payment Card Industry (PCI) compliance, and missing patches, our technical co-founder wanted to make it easier fo avoid these findings
- The existing risk visibility tools for insurance underwriters took a shallow look at Internet-facing risks. They -- along with all businesses -- need a deeper view of the threats that could actually lead to breaches.
- Domain risks
- Operating System (OS) patches
- Application patches
- Network vulnerabilities
- Cloud vulnerabilities
- OS configurations
You can use your own logo for the console and notifications. You can also use a CNAME to automatically brand your console.
Note: you cannot currently re-proxy the CNAME to Lavawall® through Cloudflare.
Lavawall® supports the following operating systems:
Lavawall® does not currently support non systemd distributions, such as Devuan, Artix Linux, PCLinuxOS, OpenWRT, and DD-WRT. However, we will support them by the end of 2024.
In June 2024, we combined the Windows and Linux systems for a consistent experience. This added support for RedHat and MacOS.
Privacy & Security
However, we do allow passwords and use passwords as part of the zero-knowledge encryption for your clients' sensitive data, such as Bitlocker keys and Personally-Identifiable Information (PII).
These passwords use Argon2id slow hashes with individual salts and peppers. They go through a few hash rounds on your computer before being sent to our servers for further hashing.
We have added an additional secure tunnel that mimics the TLS process within the public TLS tunnel. This extra tunnel provides authentication and privacy for the workstations and the Lavawall® servers to prevent attacks such as the one that took down Solar Winds.
Remote access is not enabled for read-only and audit situations.
Get In Touch
Have a quick question and don't want to talk? Send us a quick note with the form below and we'll reply within one business day.
NW Calgary:
ThreeShield Information Security Corporation
600 Crowfoot Crescent N.W., Suite 340
Calgary, Alberta
T3G 0B4
SE Calgary:
ThreeShield Information Security Corporation
105, 11500 - 29th St. SE
Calgary, Alberta
T2Z 3W9
Canada